 aiFWall
aiFWall
Distributed, Contextual, Self-learning AI Security.
A guide for purchasing Al security solutions must address the distinct challenges that arise from using Al technology, rather than relying on traditional security methods.
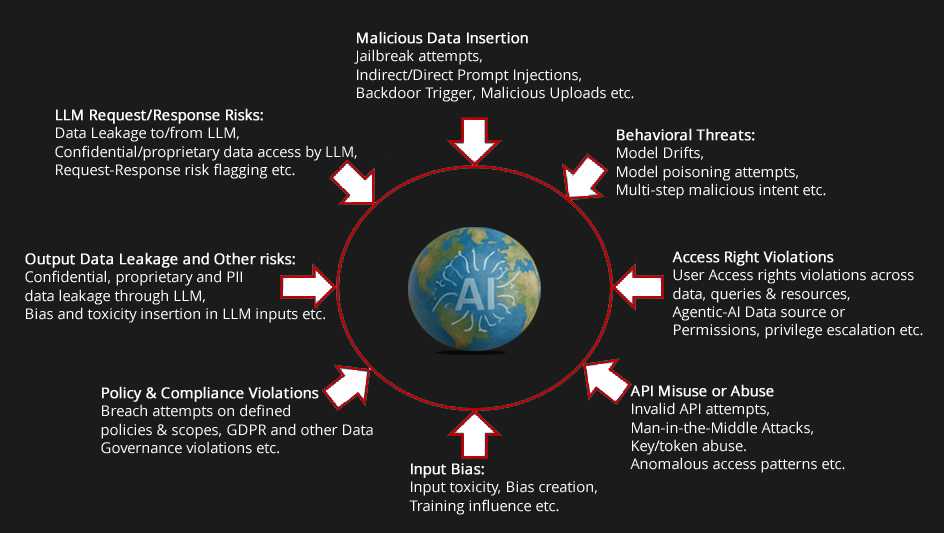
Artificial Intelligence (Al) is being deeply integrated into enterprise operations, driving efficiencies in customerservice, finance, supply chain management, and product innovation. However, as organizations expand theirreliance on Al, they also inherit a new set of risks. These include threats unique to Al models-such as promptinjections, data extractions, model poisoning and other risks -as well as traditional cybersecurity risks manifestedin new forms.
A comprehensive Al security platform should provide continuous protection across the entire Al lifecycle.
A comprehensive Al security platform should include thefollowing core capabilities:
As you evaluate potential solutions, be prepared with these questions to ensure you select the best fit for your organization:
Understand the new Al threat landscape
When assessing vendor solutions, look for thefollowing capabilities: